Solutions by Topic
The 5 Pillars of Cybersecurity, comprising of; Internal Threat Monitoring, External Threat Mapping, Open Source Intelligence (OSINT), Incident Response and Protection, provide a comprehensive, multi-layered defence strategy designed to safeguard users and organisations in an increasingly hostile digital landscape.
By integrating these pillars, organisations move from a purely reactive stance to a proactive and predictive security posture.
Internal Threat Monitoring and Protection act as the first line of defence, securing data from both accidental leaks and malicious external breaches. Meanwhile, External Threat Mapping and OSINT (Dark Web Analysis) provide critical foresight, identifying potential attacks before they hit the perimeter. Finally, a robust Incident Response framework ensures that if a breach does occur, the impact is minimised and recovery is immediate.
Together, these pillars create a resilient ecosystem that protects sensitive data, ensures business continuity, and builds digital trust.

Internal Threat Monitoring
This pillar concentrates on identifying and mitigating risks that originate from within the organisation. By leveraging Artificial Intelligence (AI) and Machine Learning (ML), the platform enables the early detection of “low and slow” attacks, including anomalous login detection, privileged escalation alerts, and credential misuse identification.
Key capabilities include User and Entity Behaviour Analytics (UEBA) for profiling suspicious activity, Data Leakage Prevention (DLP) to stop unauthorised data transfers, and privileged access control to secure critical administrative accounts.
The architecture also supports advanced measures such as blocking screenshots, scanning file uploads, and monitoring USB data transfers to prevent internal data exfiltration.
External Threat Mapping
To secure the digital perimeter, this pillar involves deeply understanding and mapping the external digital landscape to uncover potential vulnerabilities. It utilises a Geo-Spatial Threat View to visualise threats globally and employs targeted sector risk heatmaps to assess danger levels across different industries.
This pillar proactively manages the external attack surface through automated threat severity scoring and detailed threat actor profiling, helping the organisation anticipate risks such as state-backed cyber espionage, Distributed Denial-of-Service (DDoS) attacks, and supply chain compromises. It also includes continuous monitoring of the external attack surface to discover exposed assets and sync vulnerability data.

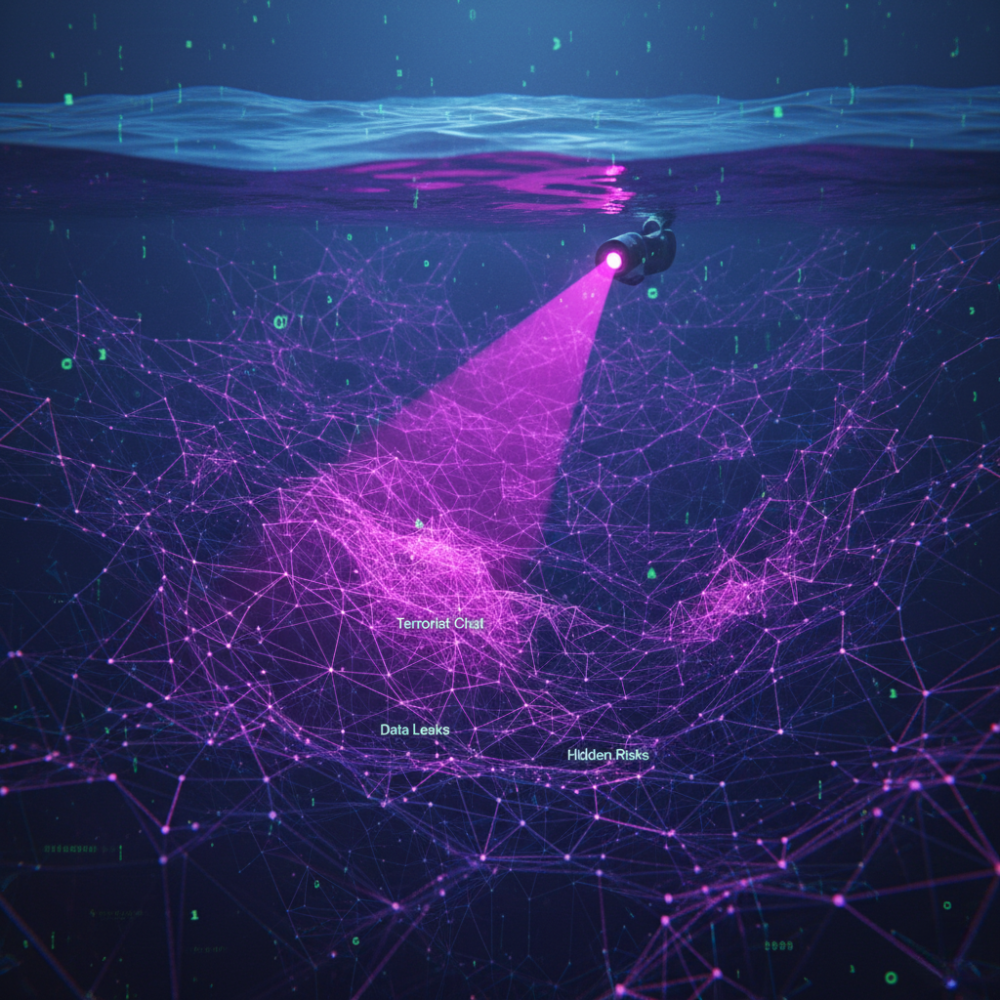
Physical Threat Analysis
This pillar harnesses Open-Source Intelligence (OSINT) and dark web monitoring to expose hidden threats before they can be executed. It features advanced surveillance capabilities, including the tracking of terrorist chat channels, alerts for dark web data leaks, and broad media scanning to detect emerging campaigns.
By utilising Natural Language Processing (NLP) and sentiment and intent analysis, the system can identify the motivation behind potential attacks. Additionally, this pillar integrates complex technologies such as facial and fingerprint recognition with identity analytics to correlate physical and digital identities for a comprehensive threat view.
Incident Response
Effective recovery is critical, and this pillar outlines the standard operating procedures for responding to and recovering from cyber incidents efficiently. It emphasises incident prioritisation, cross-agency coordination, and automated remediation actions to minimise downtime.
The platform utilises Security Orchestration, Automation, and Response (SOAR) automation playbooks and a digital forensic toolkit to ensure a swift, evidence-driven response to any crisis. It is supported by a Crisis Communication Hub to manage information flow during an event and uses AI models for impact and severity prediction to forecast the potential blast radius of an attack.


Protection and Prevention
The final pillar emphasises proactive, multi-layered measures to prevent cyber threats and safeguard digital assets before damage occurs. This comprehensive layer includes Next-Generation AI Firewalls, automated malware kill systems, and Zero Trust Network Access (ZTNA) to strictly control network entry.
It also deploys an anti-ransomware shield to stop encryption attacks and ensures robust endpoint protection. The architecture covers everything from endpoint and cloud security to data integrity monitoring, ensuring that mission-critical assets remain secure against evolving threats.
